Wana Decrypt0r 2.0 .WNCRY File Virus (Restore Files)

This article is created to help you remove the .WNCRY Wana Decrypt0r 2.0 ransomware infection (new WannaCry variant) and restore files encrypted with the .WNCRY file extension.
A new ransomware, called Wana Decrypt0r 2.0 by malware hunters has been reported to encrypt files on the computers infected by it. The ransomware virus uses the .WNCRY file extension and it is basically reported to be a new version of the WannaCry also known as WCry family of ransomware viruses. The infection drops a ransom note, named @[email protected] and changes the wallpaper as well as adds software with instructions for paying the ransom. In case you have become a victim of this ransomware infection, we strongly recommend to read the following article thoroughly.

| Name |
.WNCRY |
|
| Type | Ransomware | |
| Short Description | New May 2017 version of the WannaCry ransomware viruses. Encrypts files and then demands victims to pay a hefty ransom fee in order to restore the encrypted files. | |
| Symptoms | Files are encrypted with the .WNCRY file extension added to them. In addition to this a ransom note is added, named @[email protected]. Also adds a lockscreen, named “Wana Decrypt0r 2.0”. | |
| Distribution Method | Via an Exploit kit, Dll file attack, malicious JavaScript or a drive-by download of the malware itself in an obfuscated manner. | |
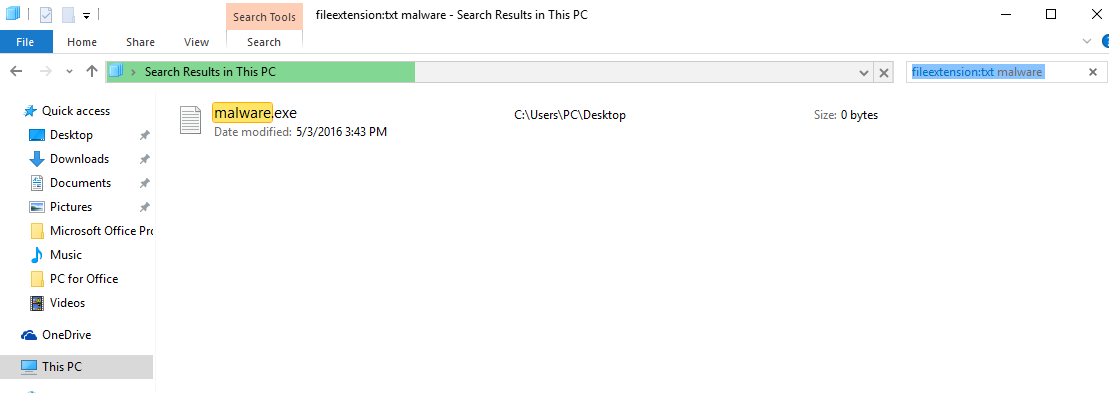
| Detection Tool | See If Your System Has Been Affected by .WNCRY
Download
Malware Removal Tool
|
|
| User Experience | Join our forum to Discuss .WNCRY. | |
| Data Recovery Tool | Windows Data Recovery by Stellar Phoenix Notice! This product scans your drive sectors to recover lost files and it may not recover 100% of the encrypted files, but only few of them, depending on the situation and whether or not you have reformatted your drive. |
UPDATE MAY 2017 We have summed up potential methods by which you could theoretically try and restore your files. We have also included new information about how does this virus spread. The instructions are in the following article.

.WNCRY Virus – How Does It Spread
Similar to the previous .wcry variant , this ransomware iteration may also use the very same methods to spread. They are connected with the usage of different types of tools used specifically to distribute malicious files and URLs without being detected:
- The ETERNALBLUE and DOUBLEPULSARE Exploits leaked by the ShadowBrokers in a leak, called “Lost in Translation” which happened back in April 2017
- Spamming software (spam bots, crawlers, etc)
- Pre-configured list of e-mail addresses of potential victims to which spam mail may be sent.
- Intermediary malware to conduct the infection.
- A set of C2 servers and distribution domains for command and control and the download of .WNCRY file virus’ payload.
Even though the WanaCrypt0r 2.0 ransomware may spread via torrent websites, fake updates or other fake setups and executables uploaded on shady hots, the virus’s primary method of spreading may be via convincingly created e-mails. Such e-mails aim to get victims to click on a malicious e-mail attachment and hence become infected with the .WNCRY file virus.
The attachments may usually be .js, .exe or other type of executable files, but in some situations they are also related with malicious macros. These malicious macros may be activated once the user enables the content on a document. Here is how this infection process is conducted:
The first infections of Wana Decrypt0r 2.0 have been in Germany, Russia, Taiwan, Turkey, Kazakhstan, Indonesia, Vietnam, Japan, Spain, Ukraine and the Philippines. But the countries number may rise very rapidly soon, since this pattern shows global distribution campaign.

.WNCRY File Virus How Does It Work
The main activity of the Wana Decrypt0r 2.0 ransomware virus after infection is to drop an embedded file into the folder where the infection file is located. The file is a password protected .zip, named wcry.zip. It has the following contents:
- b.wnry
- c.wnry
- r.wnry
- s.wnry
- t.wnry
- u.wnry
- taskse.exe
- taskdl.exe
The Wana Decrypt0r 2.0 ransomware’s infection file will then extract those zipped files into a folder and begin to connect to the download web page of the TOR web browser. From there, the .Wana Decrypt0r 2.0 virus may connect to multiple command and control servers:
- 57g7spgrzlojinas.onion
- xxlvbrloxvriy2c5.onion
- 76jdd2ir2embyv47.onion
- cwwnhwhlz52maqm7.onion
Then, Wana Decrypt0r 2.0 prepares for encrypting vital victim files. To do this, it runs an administrative command in Windows in order to obtain Administrator functions:
→ icacls . /grant Everyone:F /T /C /Q
Then, the Wana Decrypt0r 2.0 virus shuts down the following Windows System processes from the Task Manager:
→ Mysqld.exe
Sqlwriter.exe
Sqlserver.exe
MSExchange
Microsoft.Exchange
The payload may consist of multiple different types of files. Some of those files may modify the Windows Registry Editor and target the following sub-keys:
→ HKCU\Software\Microsoft\Windows\CurrentVersion\Run\
HKCU\Software\WanaCrypt0r\
HKCU\Software\WanaCrypt0r\wd
HKCU\Control Panel\Desktop\Wallpaper
In those keys, custom value strings with data in them may be input so that it is possible for the ransomware to run on system startup and begin encrypting files on boot.
In addition to the activity of WanaCrypt0r .WNCRY infection may be to delete the shadow volume copies and eradicate all chances of reverting your files via backup on the infected computer. This is done by executing the following administrative Windows commands:
→ vssadmin delete shadows /all /quiet
wmic shadowcopy delete
bcdedit /set boostatuspolicy ignoreallfailures
bcdedit /set {default} recoveryenabled no & wbadmin delete catalog -quiet
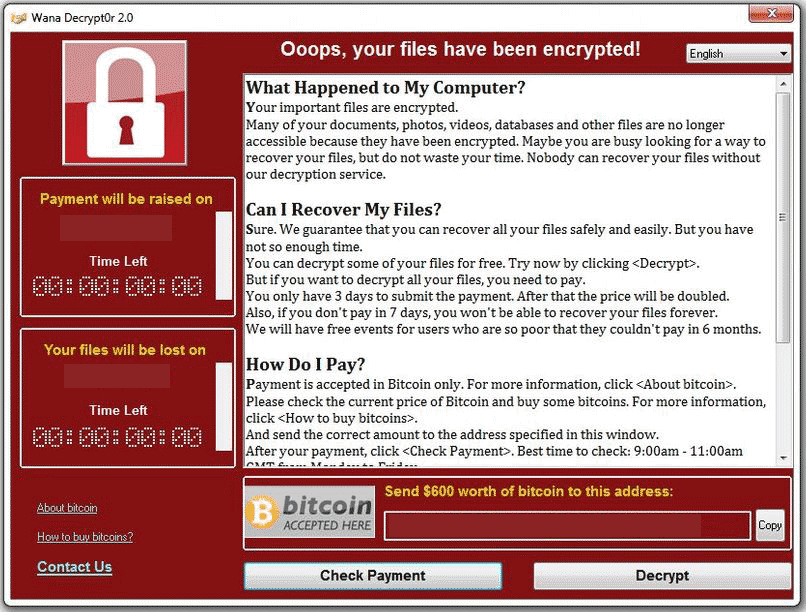
In addition to this activity, WannaCry .WNCRY virus also drops a program, named @[email protected] that has an actual timer with advanced instructions on how to pay the ransom. This program is called “Wana Decrypt0r 2.0” and it’s message looks like the following:
After the timer on this program runs out the cost of the ransom payoff may double, according to the scareware messages and the previous version, also using this software.
Another action the program makes is that it also changes the wallpaper on the victim’s computer with the following message:
Ooops, your important files are encrypted.
If you see this text, but don’t see the ”Wana Decrypt0r” window,
then your antivirus removed the decrypt software or you deleted it from your computer.
If you need your files you have to run the decrypt software.
Please find an application file named “@[email protected]” in any folder or restore from the antivirus quarantine.
Run and follow the instructions!

.WNCRY File Virus – Encryption Process
Two encryption algorithms may be used for this specific ransomware infection. One of those is known as AES (Advanced Encryption Standard) and may be used in 128-bit of strength. It is one of the strongest ciphers and cannot be decrypted unless the criminals make a mistake in the encryption code. It may generate a symmetric key, called FEK key after encryption. This key may be the only method to decrypt the files because with it the process can be reversed.
In addition to this, another cipher known as Rivers-Shamir-Adleman or RSA is also used in combination with the AES cipher in order to generate unique public and private keys for each of the files. This makes the decryption of each file separate and very difficult and unique process.
For the encryption process, the .WNCRY virus targets files that are widely used. These files are usually the following:
→ .ldf, .sln, .suo, .cpp, .pas, .asm, .cmd, .bat, .vbs, .dip, .dch, .sch, .brd, .jsp, .php, .class, .wav, .swf, .fla, .wmv, .mpg, .vob, .mpeg, .asf, .avi, .mov, .mkv, .flv, .wma, .mid, .djvu, .svg, .psd, .nef, .tiff, .tif, .cgm, .raw, .gif, .png, .bmp, .jpg, .jpeg, .vcd, .iso, .backup, .zip, .rar, .tgz, .tar, .bak, .tbk, .PAQ, .ARC, .aes, .gpg, .vmx, .vmdk, .vdi, .sldm, .sldx, .sti, .sxi, .hwp, .snt, .onetoc2, .dwg, .pdf, .wks, .rtf, .csv, .txt, .vsdx, .vsd, .edb, .odp, .otp, .sxd, .std, .uop, .odg, .otg, .sxm, .mml, .lay, .lay6, .asc, .sqlite3, .sqlitedb, .sql, .accdb, .mdb, .dbf, .odb, .frm, .myd, .myi, .ibd, .mdf, .msg, .ost, .pst, .potm, .potx .eml, .der, .pfx, .key, .crt, .csr, .pem, .odt, .ott, .sxw, .stw, .uot, .max, .ods, .ots, .sxc, .stc, .dif, .slk, .asp, .java, .ppam, .ppsx, .ppsm, .pps, .pot, .pptm, .pptx, .ppt, .xltm, .xltx, .xlc, .xlm, .xlt, .xlw, .xlsb, .xlsm, .xlsx, .xls, .dotx, .dotm, .dot, .docm, .docb, .docx, .doc, .jar,,
After the encryption is done, the .WNCRY virus may send the decryption key to the cyber-criminals so that they can create a custom decrypter for the victim which will be sent back to him once the ransom is paid. Paying the ransom, however is highly inadvisable.
The files have an added .WNCRY file extension to them which is unique for the infection. The files may appear like the following and cannot be opened with any software:

Remove WanaCrypt0r 2.0 and Restore .WNCRY Encrypted Files
In order to remove .WNCRY ransomware, we urge you to backup your files first by creating copies of them and then to proceed with the removal. One method to remove it is if you follow the removal instructions at the bottom of this article. They are carefully created in order to help you delete all the files by isolating the .WNCRY virus first. If you want to automatically and completely remove the WanaCrypt0r 2.0 threat, recommendations are to focus on removing the ransomware infection with the aid of an advanced anti-malware tool which will make sure the removal process is swift.
For the recovery of your files, we urge you to try out the alternative methods for restoring encrypted files. They may not fully recover all your files but may restore most of your encrypted files in the right scenario. You can find the methods In step “2. Restore files encrypted by .WNCRY” below.
Manually delete .WNCRY from your computer
Note! Substantial notification about the .WNCRY threat: Manual removal of .WNCRY requires interference with system files and registries. Thus, it can cause damage to your PC. Even if your computer skills are not at a professional level, don’t worry. You can do the removal yourself just in 5 minutes, using a malware removal tool.
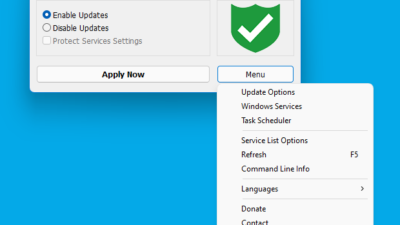
Automatically remove .WNCRY by downloading an advanced anti-malware program
1
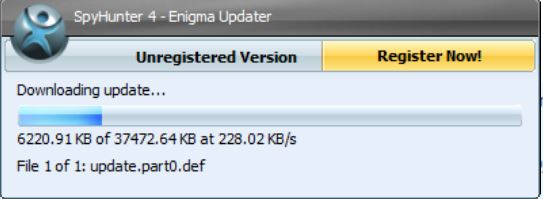
Remove .WNCRY with SpyHunter Anti-Malware Tool
 1. Install SpyHunter to scan for and remove .WNCRY.
1. Install SpyHunter to scan for and remove .WNCRY. 2. Scan with SpyHunter to Detect and Remove .WNCRY.
2. Scan with SpyHunter to Detect and Remove .WNCRY.It is highly recommended to run a scan before purchasing the full version of the software to make sure that the current version of the malware can be detected by SpyHunter.
Step 2: Guide yourself by the download instructions provided for each browser.
Step 3: After you have installed SpyHunter, wait for it to automatically update.
2
Restore Files Encrypted by .WNCRY
Ransomware infections like .WNCRY aim to encrypt your files using an encryption algorithm which may be very difficult to directly decrypt. This is why we have suggested several alternative methods that may help you go around direct decryption and try to restore your files. Bear in mind that they may not be 100% effective but they may help you little or a lot in some situations.
Method 1: Scanning your drive’s sectors by using Data Recovery software.
Another method of restoring your files is by trying to bring back your files via data recovery software. Here are some suggestions for preferred data recovery software solutions:
Method 2: Trying Kaspersky and EmsiSoft’s decryptors.
If the first method does not work, we suggest trying to use decryptors for other ransomware viruses, in case your virus is a variant of them. The two primary developers of decryptors are Kaspersky and EmsiSoft, links to which we have provided below:
Urgent! It is strongly advisable to first remove the .WNCRY threat before attempting any decryption, since it may interfere with system files and registries. You can do the removal yourself just in 5 minutes, using an advanced malware removal tool.
Method 3: Using Shadow Explorer
To restore your data in case you have backup set up, it is important to check for shadow copies in Windows using this software if ransomware has not deleted them:
Method 4: Finding .WNCRY decryption key while it communicates it via a network sniffing software.
Another way to decrypt the files is by using a Network Sniffer to get the encryption key, while files are encrypted on your system. A Network Sniffer is a program and/or device monitoring data traveling over a network, such as its internet traffic and internet packets. If you have a sniffer set before the attack happened you might get information about the decryption key. See how-to instructions below:
3
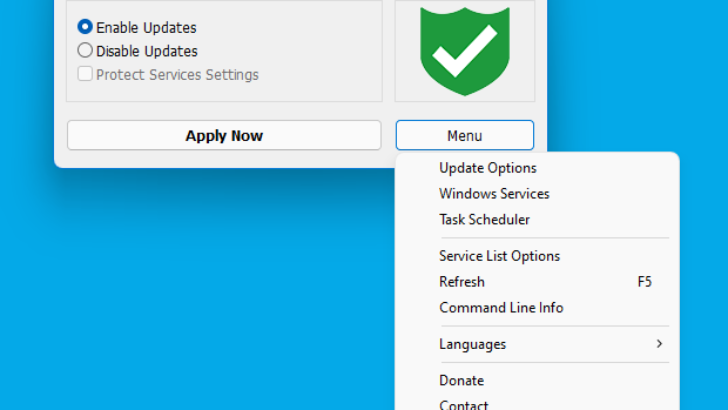
Remove .WNCRY Using Other Alternative Tools
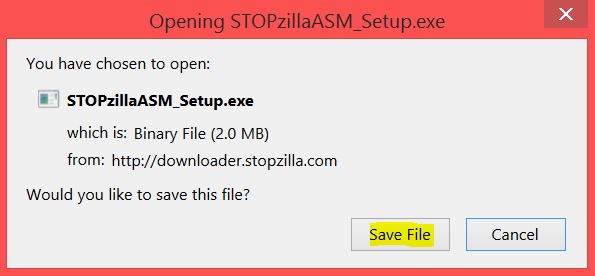
 STOPZilla Anti Malware
STOPZilla Anti MalwareStep 1: Download STOPZilla by clicking here.
Step 2: A pop-up window will appear. Click on the ‘Save File’ button. If it does not, click on the Download button and save it afterwards.
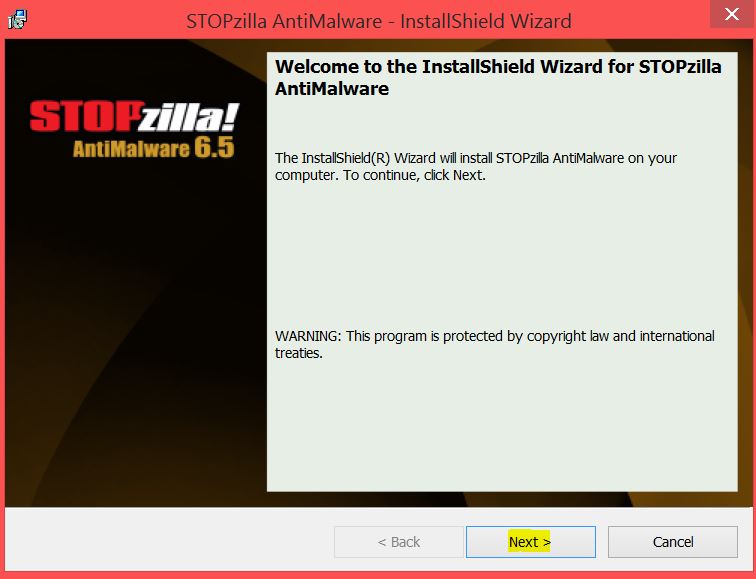
Step 3: After you have downloaded the setup, simply open it.
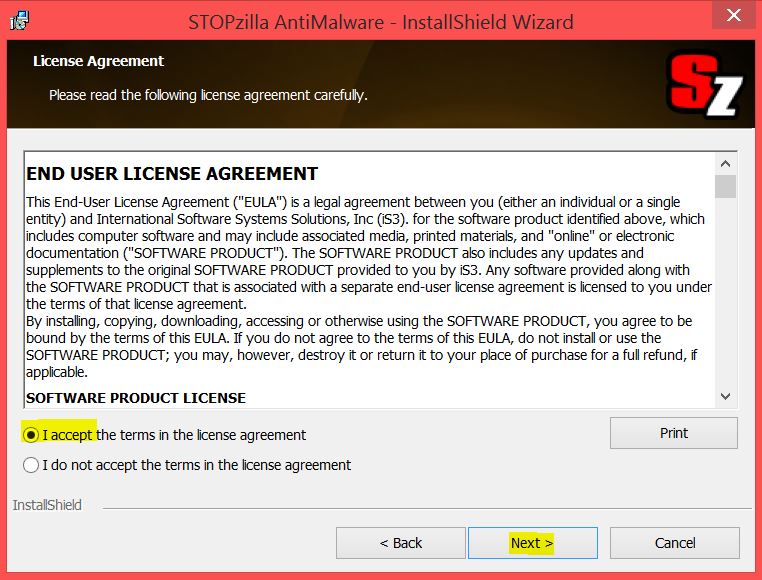
Step 4: The installer should appear. Click on the ‘Next’ button.
Step 5: Check the ‘I accept the agreement’ check circle if not checked if you accept it and click the ‘Next’ button once again.
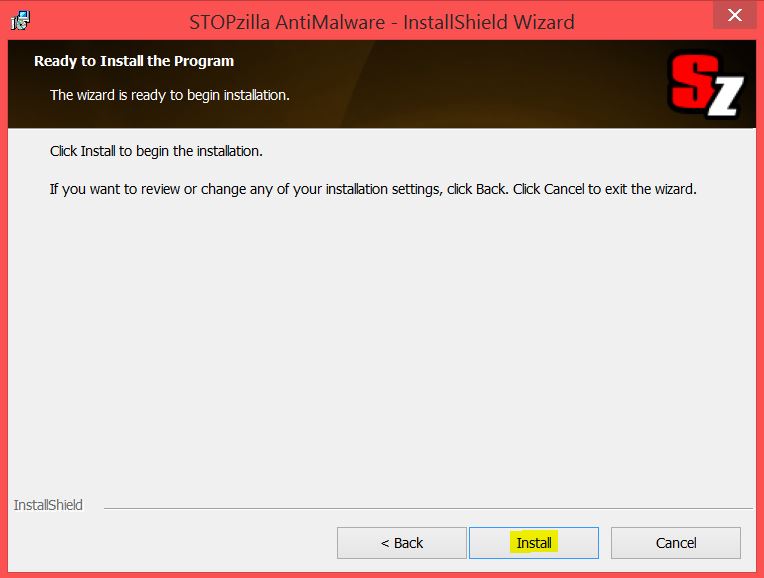
Step 6: Review and click on the ‘Install’ button.
Step 7: After the installation process has completed click on the ‘Finish’ button.2. Scan your PC with STOPZilla Anti Malware to remove all .WNCRY associated files completely.
Step 1:Launch STOPZilla if you haven’t launched it after install.
Step 2: Wait for the software to automatically scan and then click on the ‘Repair Now’ button. If it does not scan automatically, click on the ‘Scan Now’ button.
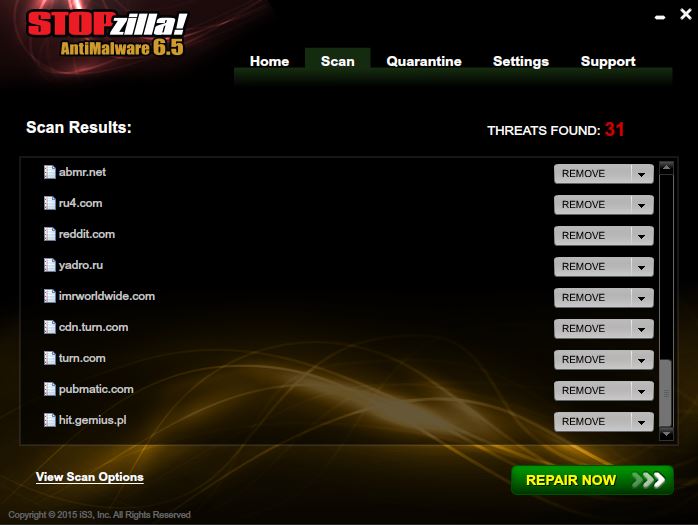
Step 3: After the removal of all threats and associated objects, you should Restart your PC.
qoute source: http://sensorstechforum.com/wncry-file-virus-remove-restore-files/


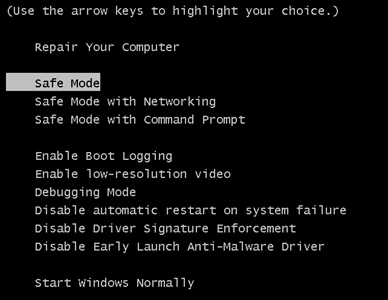
 1. For Windows 7,XP and Vista.
1. For Windows 7,XP and Vista. 2. For Windows 8, 8.1 and 10.
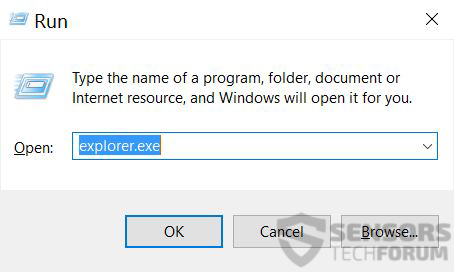
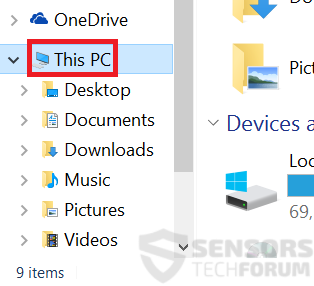
2. For Windows 8, 8.1 and 10. Fix registry entries created by .WNCRY on your PC.
Fix registry entries created by .WNCRY on your PC.